August 17, 2021
Using the MITRE ATT&CK Framework
Knowing how to apply this knowledgebase of security tactics and techniques will help better protect your organization.

You may have heard about MIRE ATT&CK since it is being integrated as a metric in many tools and talked about as a way to measure your network ‘s defenses, but not know what it is. MITRE ATT&CK is a matrix of common methods that adversaries use to break into, steal data from or otherwise cause damage an organization’s network and systems. This matrix can be used by organizations large and small to analyze their capabilities against many different adversaries with various levels of sophistication.
Discover how CDW services and solutions can help address your security needs.
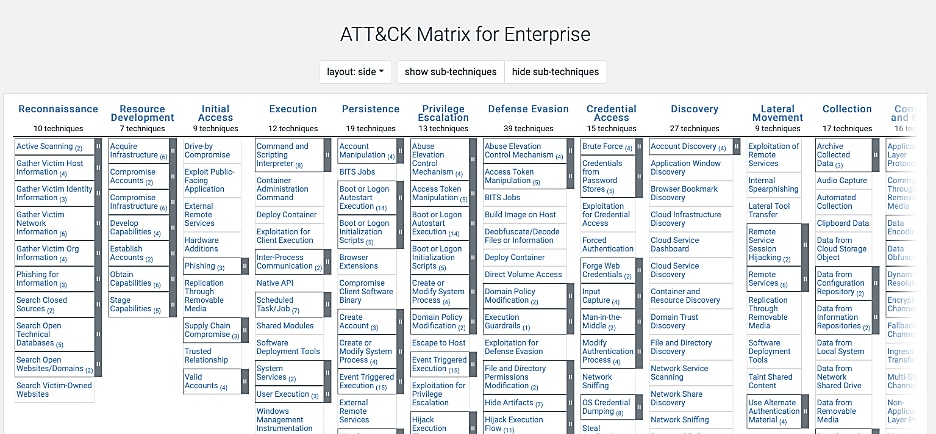
To help organize common adversarial methods, the ATT&CK matrix is organized into tactics and techniques.
- Tactics are a category describing an attacker's goal, for example, reconnaissance, collecting data about a target.
- Techniques are a high-level description of the actions an attacker would take. A technique can be broken down into a sub-technique if there are similar actions that can be taken. Each technique has detailed information about what an adversary does.
Now that you understand the major categories in ATT&CK, let’s look at how it can help you defend your network.
How Can ATT&CK Knowledge Help Me?
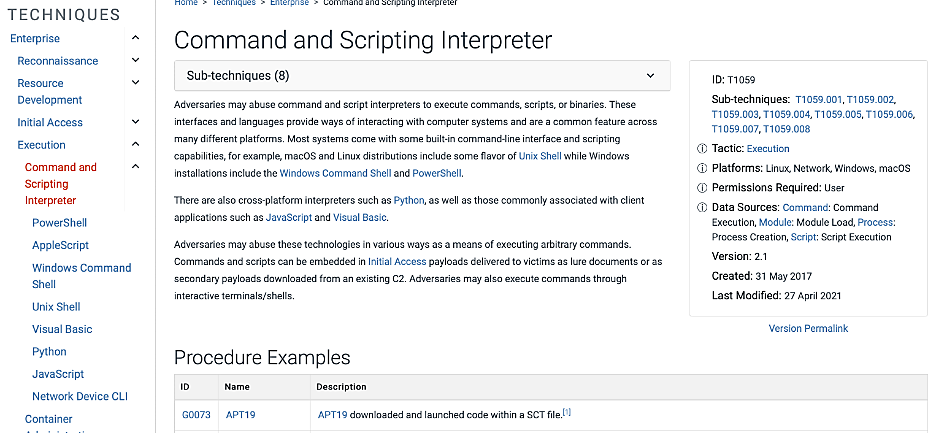
The information about tactics and techniques is interesting at a high level, but you may ask yourself, how do they help me as a defender? This question brings us to the information in each technique. The techniques contain details such as adversary procedures, defensive mitigation and detection methods.
- Procedures are included in each technique and offer an example of how an adversary executes the method. ATT&CK uses real-world examples from adversaries in the techniques.
- The mitigations provide examples of systems architecture, tools and defensive procedures that can be deployed to protect against the adversary's technique. Each of these recommendations can help you prepare for the attack methods.
- The detection section describes ways to see the technique in action. It is essential to have viability of attacks occurring. You do not want to get into a case of Schrödinger's defenses, where you can't measure your defenses working, so you don't know if they are working. The information in MITRE ATT&CK is invaluable in helping defenders identify where they need to improve their defenses.
ATT&CK’s breadth of information provides your organization with another way to prepare your network against adversaries. It provides you criteria to evaluate your people, processes and tools to make sure your organization can detect and response to attacks from adversaries big and small.
Recent Update
At the end of April 2021, Mitre released version 9 of ATT&CK, including many enhancements. There are three key areas that were updated.
- Data Sources and Components
- Consolidate cloud providers
- Containers
How Can CDW Help?
After looking at all the information in ATT&CK, it can be overwhelming. If you need help in preparing you network defenses, CDW has many services that can help your organization. A few of CDW's services that can help hone your defenses include:
- Incident Response Preparedness Services
- Rapid Security or Comprehensive Security Assessments
- Security Maturity Assessment
For more information, reach out to your CDW Account Manager or visit the CDW’s Amplified Security Site.
